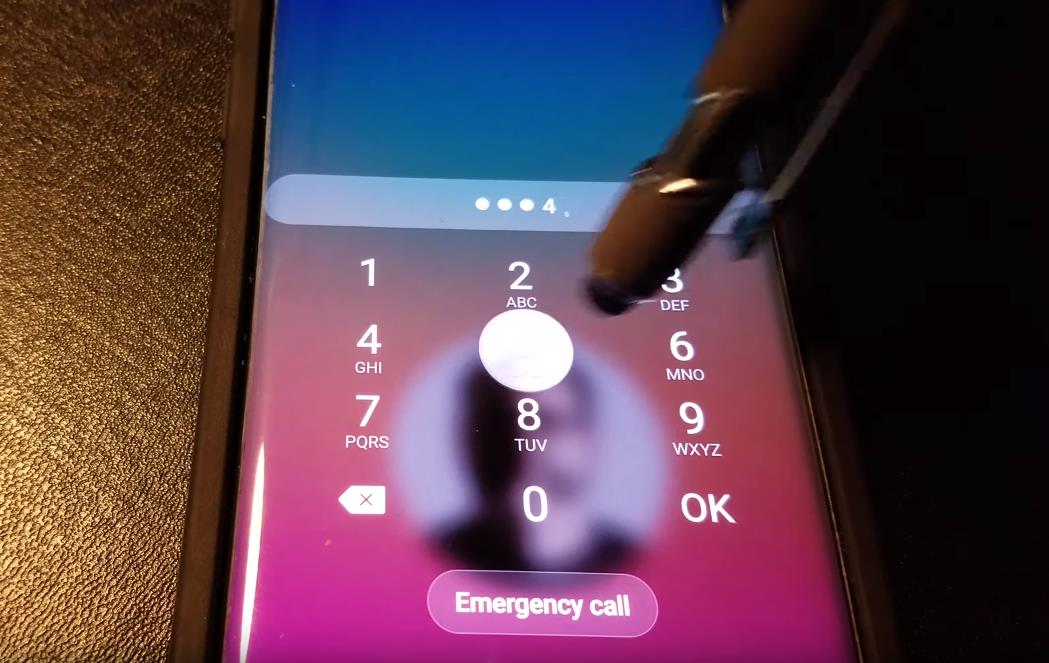
Hackers Can Steal Your Passwords, Emails, And Texts By Listening As You Type On Your Smartphone
Hackers may be able to read whatever you type on a smartphone – by listening in via the device’s microphone.
When humans tap on a touchscreen, they generate sound waves that are often strong enough to be picked up by the same device’s nearby microphone/s. Because each particular character on a device’s virtual keyboard appears consistently in the same place whenever the keyboard is displayed, and because each character appears in a different location than other characters, the sound waves that users generate when they hit any particular character travel different distances through the phone and the air in order to reach the microphone/s than do the waves of other characters. As a result, a device’s microphone/s may consistently hear a slightly different sound for each particular character that a user taps.
As a result of such a physics-induced phenomenon, researchers at the UK’s University of Cambridge and Sweden’s Linköping University were able to use computers to analyze the various vibrations heard by device microphones, and, as a result, to correctly calculate 27 out of 45 passwords typed on a smartphone, and 19 out of 27 passwords typed on a tablet.
While there are presently no known strains of malware that utilize such “listening” techniques to steal passwords or other material typed on a smartphone or tablet, there is no assurance that either criminals or governments (military, intelligence agencies, etc.) are not already using such techniques. (When academic researchers publish a cybersecurity-related vulnerability, there is always the risk that governments or criminals discovered the problem sooner and are already exploiting it – since criminals and government agencies do plenty of research, and rarely, if ever, publicize any of their discoveries.)
In fact, we know that, going back decades, governments have utilized acoustic analysis to “read” what someone is typing – during the Cold War, for example, spy agencies were sometimes able to determine what someone was typing on a manual typewriter by listening to the sounds generated when the inked characters impacted the paper – the different lengths of the arms holding the metal characters, as well as the different shapes of the characters themselves, caused the sound generated by each particular character striking paper to vary slightly from those generated by other characters doing likewise.
Are intelligence agencies are already using similar techniques to read what people type on smartphones? Clearly, those who know will not say.
In any case, regardless of whether such listening techniques are already in use, with the publication of the Cambridge – Linköping paper, it is likely that such techniques will be used by many parties at some point in the future.
How can you stay secure?
1. Keep your phone secure
At least as far as we know from the current research, outsiders can only listen to what you type if they have access to the microphone on your device, which they are unlikely to obtain if you properly secure your device. For some tips on how to secure your device please download the free checklist: 10 Important and Easy Steps to Secure Your Smartphone and Laptop.
2. Use bogus tapping sounds when necessary.
Eventually, we will likely see features within smartphone keyboards that generate bogus tapping sounds. Such features may also appear in third-party apps. If spying-via-listening becomes a problem, such technology might be useful – especially since it could also help address the risk that adequate listening might be possible using sensitive microphones on external devices that need not be infected with malware.
3. Do not “type” anything sensitive with “voice to text.”
If there is any chance that criminals have access to your microphone, and you type with voice to text, the crooks are likely to hear everything that you type. This recommendation is true regardless of the current research.
Hackers may be able to read whatever you type on a smartphone – by listening in via the device’s microphone. #CyberSecurity #Privacy Click To Tweet










 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.