-
CyberSecurity
Hackers Create Master Keys For Millions Of Hotel Rooms
April 29, 2018Security researchers have successfully created master keys that can open millions of hotel rooms, as well...
-
Toys / Children
Malty the Blue Tiger: New, Bilingual Book Teaches Important Lessons and a Second Language
April 29, 2018Scientists teach that there are significant benefits of raising a child to speak more than one...
-
CyberSecurity
Police Attempt To Unlock Dead Man’s Phone By Using His Finger
April 23, 2018According to published reports, police in Largo, Florida, USA, went to the funeral home housing the...
-
CryptoCurrency / BlockChain / ICO
Cryptocurrency Wallets 101: No, You Can’t Store Cryptocurrency In Them (1 minute video)
April 23, 2018Today’s short cybersecurity video: Cryptocurrency Wallets 101: Key-Rings, Not Wallets
-
CyberSecurity
12 Types of Business Data That Require Strong Cybersecurity
April 20, 2018As is obvious from seemingly incessant news reports of data breaches, businesses often do not adequately...
-
CyberSecurity
Facebook, Microsoft, Cisco, Dell, and 30 Other Global Companies Make Joint CyberSecurity Pledge
April 17, 201834 global technology and security companies today announced a Cybersecurity Tech Accord, likely the largest-ever formal...
-
CryptoCurrency / BlockChain / ICO
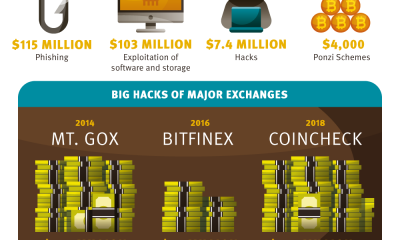
How Criminals Steal Cryptocurrency (InfoGraphic)
April 15, 2018Security is a big concern in the world of cryptocurrency. Here is some information on how...
-
CyberSecurity
Google Loses Landmark “Right to be Forgotten” Case
April 13, 2018A European businessman has won a UK High Court action that demands that Google remove from...
-
CyberSecurity
Why You Should Not Borrow A Phone Charger (Short Video)
April 12, 2018Today’s short cybersecurity video: Why You Should Not Borrow A Phone Charger
-
CyberSecurity
How to Avoid Dangerous LinkedIn Scams
April 11, 2018LinkedIn is, of course, a powerful social network that delivers many professional benefits to its users....


















 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.