CyberSecurity
-
Police Attempt To Unlock Dead Man’s Phone By Using His Finger
April 23, 2018According to published reports, police in Largo, Florida, USA, went to the funeral home housing the...
-
Cryptocurrency Wallets 101: No, You Can’t Store Cryptocurrency In Them (1 minute video)
April 23, 2018Today’s short cybersecurity video: Cryptocurrency Wallets 101: Key-Rings, Not Wallets
-
12 Types Of Data That Businesses Need To Protect But Often Do Not
April 20, 2018As is obvious from seemingly incessant news reports of data breaches, businesses often do not adequately...
-
Facebook, Microsoft, Cisco, Dell, and 30 Other Global Companies Make Joint CyberSecurity Pledge
April 17, 201834 global technology and security companies today announced a Cybersecurity Tech Accord, likely the largest-ever formal...
-
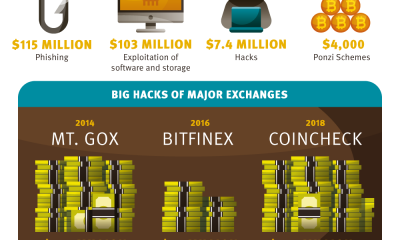
How Criminals Steal Cryptocurrency (InfoGraphic)
April 15, 2018Security is a big concern in the world of cryptocurrency. Here is some information on how...
-
Google Loses Landmark “Right to be Forgotten” Case
April 13, 2018A European businessman has won a UK High Court action that demands that Google remove from...
-
Why You Should Not Borrow A Phone Charger (Short Video)
April 12, 2018Today’s short cybersecurity video: Why You Should Not Borrow A Phone Charger
-
How to Avoid Dangerous LinkedIn Scams
April 11, 2018LinkedIn is, of course, a powerful social network that delivers many professional benefits to its users....
-
Symmetric and Asymmetric Encryption – What Is The Difference? (Short Video)
April 10, 2018Today’s short cybersecurity video: What is the Difference Between Symmetric and Asymmetric Encryption?
-
8 Ways to Protect Yourself From Scams and Data Collection on Social Media
April 9, 2018Here are eight ways to avoid scams on social media, and to help protect your personal information...

















 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.