A Sign Of The Times: Even Scammers Are Using Terrible Passwords
Once in a while, a scam email successfully evades detection by various commercial filtering technologies in use in my office, and arrives in my inbox. Often, the messages that make it through are either targeted attacks, generic attacks personalized with information lifted from public databases and/or stolen during breaches of major corporations, or especially creative scams utilizing well-written content. Today, however, a half-dozen variants of the following email somehow arrived; this particular message appears interesting enough to share with my readers, because certain elements stand out – and, perhaps, teach us an important lesson:
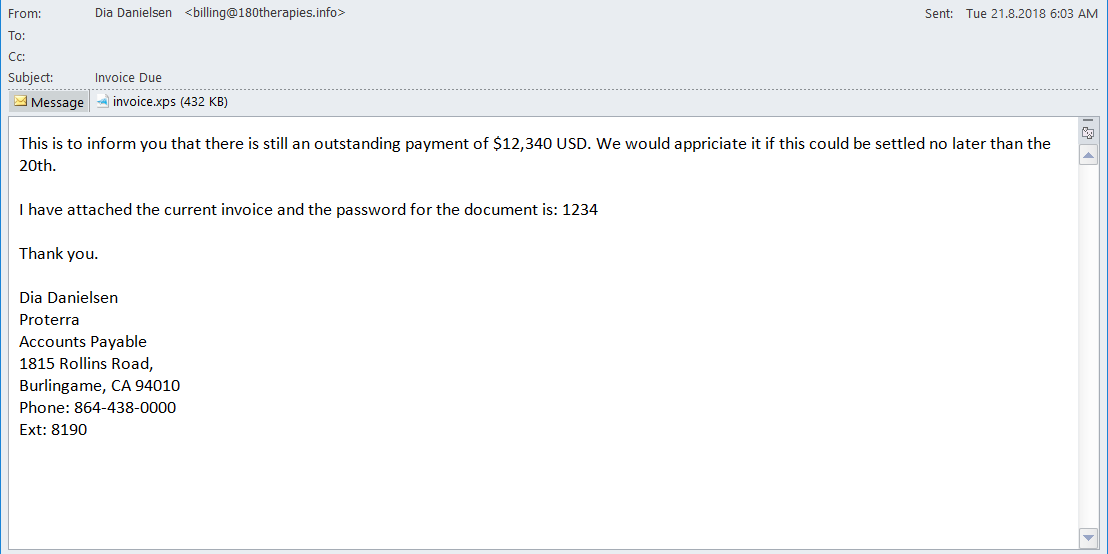
As you can see from the screenshot below, the email asks that the user open an attached invoice and issue payment on it – of course, in reality, unless one is a masochist seeking to infect his or computer with malware, he or she should not open the file, and, obviously, nobody should issue payment to anyone related to this scam.
What is particularly intriguing about this scam email is that while the name of the “sender” changes between variants, the bogus invoice amounts listed in all of the variants are identical – $12,340 – and the passwords to unlock the corresponding attachments are also all the same, 1234.
It seems that some criminals may be attempting to exploit the fact that, to info-security professionals’ chagrin, 1234 remains one of the world’s most popular (and hence, realistic looking) passwords; perhaps the “matching” dollar figure was chosen for simplicity’s sake.
Two other interesting observations about this particular scam email:
1. The “sender’s” name follows the pattern that I previously mentioned is often utilized by scammers – overly American sounding first and last names that begin with the same letter.
2. The request for payment by the 20th – sent in an email on the 21st… Or, did the crooks mean next month, and that Standard Net+30 terms now apply in the world of cybercrime…












 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.