-
CyberSecurity
Fraudulent WhatsApp Messages Circulate Telling Users That They Must Pay To Continue Using the App
July 8, 2019Over the past few days, several scam messages began circulating via WhatsApp – some of which...
-
CyberSecurity
The Government Wants To Dramatically Weaken Your Encryption. Here Is Why It Should Not.
July 3, 2019Late last week, reports emerged that, once again, senior United States government officials are contemplating seeking...
-
CyberSecurity
How to Protect Yourself From Being Robbed at an ATM
July 1, 2019Most modern bank account holders utilize ATMs on a regular basis, but few people are aware...
-
CyberSecurity
By Paying $600,000 Ransomware Demand Florida City Exposes All American Towns To Danger
June 23, 2019The city of Riviera Beach, Florida, last week agreed to pay hackers $600,000 to regain control...
-
CyberSecurity
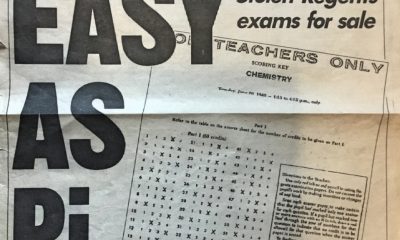
30 Years Ago Today The New York Post Shockingly Published A Stolen Exam Answer Key On Its Cover, Unknowingly Awakening An Interest In Information Security Just As The Internet Era Was To Begin
June 20, 2019Thirty years ago today, the New York Post made a dramatic move in an effort to...
-
CyberSecurity
Deja-Vu: Check Your Venmo Settings Right Now Unless You Want Everyone To See How You Spend Your Money
June 18, 2019If, like millions of other people, you use Venmo, the PayPal-owned online payment system that sports...
-
CyberSecurity
How to Securely Wipe Your Smartphone’s Data
June 17, 2019Are you planning to upgrade your smartphone, to sell your old device, or to give it...
-
CyberSecurity
Hackers Can Steal Your Passwords, Emails, And Texts By Listening As You Type On Your Smartphone
June 11, 2019Hackers may be able to read whatever you type on a smartphone – by listening in...
-
News
2 Major Social Media Trends Emerge From The 2019 Shorty Awards
May 20, 2019The world of social media recently held its eleventh annual Shorty Awards, an Oscars-type celebration that...
-
CyberSecurity
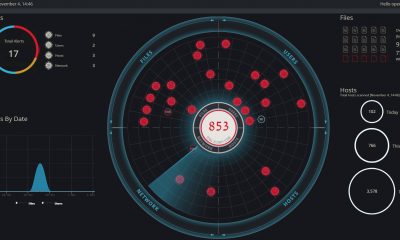
Consolidating And Strengthening Internal Environment Protection: A High-Level Look At Cynet
May 14, 2019One of the most powerful defense techniques against hackers who have invaded systems and networks is...


















 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.