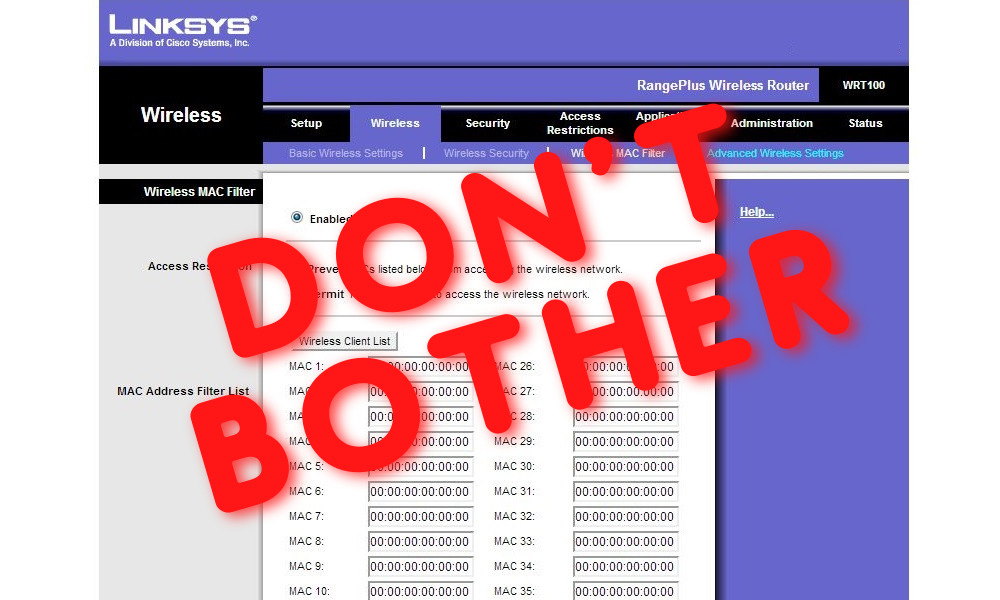
Don’t Bother Using The “Device Filter” Security Feature Offered By Your Home Network Router
The MAC address “device filtering” feature of your LAN’s router is unlikely to provide you with any significant security benefits – and, if you enable the feature, it may cause you heartaches.
Recently, I participated in a (virtual) discussion about the security of home networks – an important topic as hundreds of millions of people around the world continue to work remotely due to the ongoing COVID-19 pandemic.
During the discussion, a colleague in the field mentioned that ideally people should lock their Wi-Fi networks not only with proper encryption, but also with a MAC address filter that allows only specific authorized devices to connect to the network. MAC Addresses (media access control addresses) are unique identifiers assigned to each network interface controller; MAC address filters maintain a list of the unique MAC address assigned to the physical network connection hardware within each device authorized to connect to a network, and reject connection requests from any hardware not possessing an address in that list.
While I agree that, in theory, MAC address filtering does provide some benefits – for example, it might stop your child from connecting to your home network a malware-infected device that his or her friend brought over to your house – for multiple reasons, the cons of using MAC filtering usually far outweigh the pros of doing so. Keep in mind that:
1. You can stop unauthorized devices from connecting to your network by not giving out your Wi-Fi password; it is simple to avoid giving your children your Wi-Fi password, for example, by manually configuring the Wi-Fi settings on ther devices. Ideally, connect your children’s devices to a separate wireless network than you use (sometimes it may even be best to use your guest network).
2. If you are using proper encryption (ideally, WPA3, and, if that is not available, WPA2), the MAC address filter provides very little, if any, security benefit against hackers. Even when encrypted Wi-Fi is used, MAC addresses of connecting devices must, in some cases, be transmitted by the devices to their intended wireless access points in an unencrypted, clear text format; as such, it is trivial for a hacker to obtain the MAC addresses of devices connecting to a wireless network, to subsequently impersonate one or more such addresses on his or her own device, and to circumvent a MAC address filter. Clearly, any hacker capable of defeating your WPA- encryption is going to be more than sufficiently capable of undermining the effectiveness of your MAC address filter.
3. MAC address filtering is a pain to manage. Every time you get a new device you will have to update the filter rules on the router. In the case of many routers, all of your other devices may lose Internet connectivity when you perform such an update. (Also, note, that if you do use a MAC filter, any time that you give away, sell, or throw out a device that was allowed to connect to your network you should remove its corresponding entry from the filter rules.)
4. Many of today’s devices regularly spoof MAC addresses – which, if you use a MAC filter, can cause devices to disconnect, and to be unable to reconnect.
Of course, if you want to turn on MAC filtering in its “prevent mode” – that is, to allow all devices to connect other than some specific device or set of devices that you want to block, that is fine – but, as mentioned above, if, by enabling such a feature, you are trying to block a mischievous party from connecting to your LAN, you may be disappointed.
In short, if you want to limit access to a networked resource to only a specific device or set of devices, there are far better ways to do so than MAC filtering; you will likely derive little benefit from using a MAC address filter on your router – and it may cause you heartaches. (For full transparency and disclosure, I noted that while I do employ various sophisticated security technologies on my own LANs, I do not use MAC address filtering on any of them.)








 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.