Why You Need To Mask Sensitive Information
We are all familiar with the concept of data masking – when you enter a password online you often see the characters all appear as stars even though you have typed various letters, numbers, and special characters. In that use case, masking reduces the likelihood that people who may see your screen will be able to determine your password. In a more general sense, however, data masking refers to the process of hiding the true information contained within data records, often by replacing it with what appears to be random characters.
Data masking is often performed to protect sensitive information (such as passwords, credit card numbers, and personally identifiable information, etc.); for example: call center personnel in a retailer may need to be able to see a particular customer’s purchase records when he or she customer calls in, but, perhaps, should not be shown that person’s actual credit card information from the purchase. Likewise, when applications are being developed, coders need data for testing purposes – while that data should reflect real data, it is often inappropriate to give them access to various forms of sensitive information; true data can be masked before being handed over to them. Masking the data, of course, reduces the security risk that would be created by giving parties who do not truly need access to sensitive information access to it, especially when they would be accessing it in a non-production environment in which security controls may be far more lax than appropriate for protecting such information.
What is important to understand about data masking is that while the original information is hidden by the masking, the data must remain usable for the purposes of using and testing the systems in which it appears in masked form; masked data must, therefore, appear both real and consistent.
As the world increasingly transitions to cloud computing, masking is increasingly appropriate in production environments as well; the earlier example of a call center might be one such case. Furthermore, if financial, healthcare, or other sensitive information is going to be processed on a third-party cloud provider’s computers while in an unencrypted state – as occurs in cloud computing environments, for example – it should ideally be masked to avoid privacy problems – the provider has no business being able to view the data. Automated masking tools can mask data on the fly based on various rules – organizations need not worry about manually masking.
What could happen if data is not masked?
Imagine, for a moment, that a rogue employee working at a cloud-computing service provider accessed and misused sensitive GDPR-protected data belonging to a customer of his or her employer. Could that customer be fined by regulators for improperly protecting people’s sensitive information? What impact would the adverse press coverage of the data leak have on that customer? Would other customers of the cloud provider abandon it as a result? Would either the cloud provider or its data-breached customer suffer a decline in stock price? Suffer from expensive lawsuits? The extent of the damage is unknown – but, it could be significant.
As such, the bottom line is that while masking can be done with varying levels of complexity – from basic substitution of characters to complex, algorithmic based masking — organizations should consider the use of masking as part of their overall security strategy.
This article is sponsored by CloudMask.



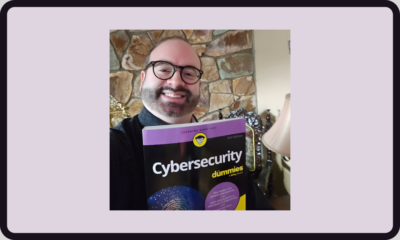






 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.