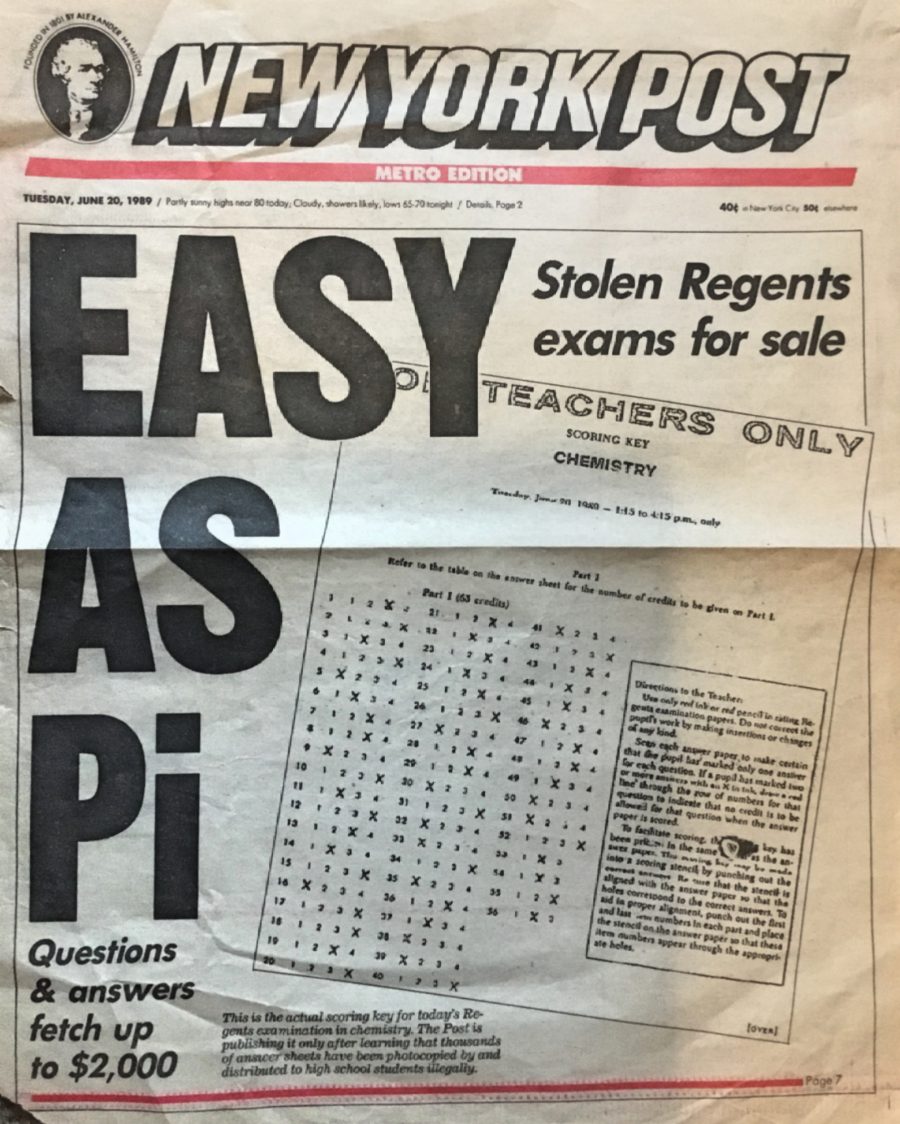
30 Years Ago Today The New York Post Shockingly Published A Stolen Exam Answer Key On Its Cover, Unknowingly Awakening An Interest In Information Security Just As The Internet Era Was To Begin
Thirty years ago today, the New York Post made a dramatic move in an effort to expose the rampant cheating taking place in certain New York schools on standardized high school exams known as “Regents” – it published on its front cover a copy of a stolen answer key to the then current day’s chemistry test, rendering the exam worthless just hours before it was scheduled to begin. As a result, the nation’s then second most populous State was forced to postpone the exam as students throughout the State sat waiting to take it.
I remember that day quite well – thankfully, I was not scheduled to take the chemistry exam, but, as a student, seeing the answer key to a test required for graduation published on the front cover of the day’s newspaper made quite an impression. It is also hard to forget the reactions of my friends who showed up at school prepared to take the test, only to be told that they would have to re-study and come back another time.
In the 30 years that have passed, the technologies that can be exploited to cheat on tests have changed dramatically; in 1989, few Americans had ever heard of, never mind used, the Internet, a cellphone, or even a digital camera. To obtain and distribute the stolen answer keys in June of 1989, those involved likely had to physically steal printed versions and manually make thousands of photocopies – few high school students in the 1980s had access to a fax machine, and even fewer had access to what might generously be termed primitive forms of email.
Advancing technologies have, of course, changed the playing field. Today, answer guides can be stolen and distributed electronically far faster, and with far less risk to the perpetrators of getting caught, than was possible a generation ago. Technology to obtain and disseminate information is ubiquitous – and the need to defend information against digital data theft has grown by many orders of magnitude. Cybersecurity has evolved from a word whose first recorded use was during that same year of 1989 into an industry measurable in the hundreds of billions of dollars.
Yet, the powerful lesson learned by a young student on that Tuesday in June 1989 still reverberates today – sensitive information must be protected throughout its lifecycle. When I arrived home after school on June 20, 1989, I spent some time wondering what vulnerabilities existed in the State’s exam distribution process, and speculating as to how the cheaters managed to exploit those weaknesses in order to steal the answer guides. As such, the Chemistry Regents may have been the first data breach about which I thought in detail. Summer camp began soon thereafter, and I moved on to other things – long relegating the stolen answer key incident to the back of my mind.
But, today, as I reflect back on the 30th anniversary of that infamous front page image, I marvel at how, 30 years later, I am still asking myself the same questions, often while examining technologies that would have been considered in 1989 to be the stuff of science fiction: What vulnerabilities exist – and how can they potentially be exploited?











 CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.
CyberSecurity for Dummies is now available at special discounted pricing on Amazon.
Give the gift of cybersecurity to a loved one.